
ecosystem
KordycepsOS is a middleware platform through which vendors deploy their autonomous modules—navigation, targeting, and swarm capabilities—across any unmanned platform. The system supports modules built on inertial navigation and computer vision, enabling missions to be carried out without reliance on GNSS signals.
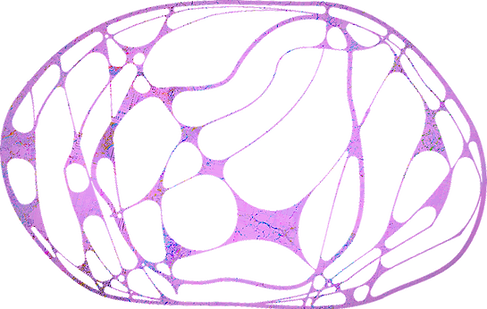
Operating
System
Edge
Cargo
Cloud
Node
Client
How it works
1
Secure Packing & Storage
The vendor packages its software into a secure Cargo container and uploads it to its own cloud storage node. The software is then ready for secure delivery, while access permissions remain under the developer’s control.
2
Mass Provisioning
Manufacturers use the Kordyceps Client for automated, bulk flashing of the OS and managing software lifecycles across deployed devices.
3
Verified Delivery
The Kordyceps Cloud performs remote attestation to verify device integrity before routing encrypted software via strict Zero-Trust protocols.
4
Volatile Execution
Software is decrypted directly into RAM and vanishes instantly upon power loss, preventing any physical data extraction or post-mortem inspection.

Partnership
Business
Technological partnership and R&D: joint development of reliable autonomous solutions and intellectual support for complex engineering projects.
Goverment
Strategic defense capability: building technological ecosystems and training engineering personnel to strengthen Ukraine's sovereignty.
Military
Technological advantage: easy-to-use systems with 90%+ accuracy that simplify operations and save lives.
FAQ
How does your autonomy system perform under active EW (Electronic Warfare) conditions?
KordycepsOS supports autonomy modules built on inertial navigation and computer vision-based visual odometry. These modules can complete a mission or return the drone to base without GNSS signals. Our OS prioritizes critical computing processes even under heavy interference.
How secure is the KordycepsOS cloud infrastructure against cyberattacks and interception?
KordycepsOS is based on Zero Trust principles. All traffic between terminals and the server is encrypted according to military standards. The system is deployed on secure servers with multi-level redundancy. For special customers, on-premise deployment is available within closed loops, physically isolated from the public network.
How does your company ensure business continuity in wartime conditions?
Production and R&D centers are geographically diversified. Digital copies of all systems are stored in cloud infrastructure across multiple jurisdictions, ensuring uninterrupted support and operation of KordycepsOS regardless of the situation at any individual location.
Does Dwarf Engineering provide scalability for large-scale government orders?
Yes. KordycepsOS is built for large-scale deployment: the Kordyceps Client automates the flashing and provisioning of thousands of devices, while its modular architecture enables production to scale without increasing per-unit integration costs.
How is the manufacturer's Intellectual Property (IP) protected when integrating your stack?
Each module runs in an isolated environment—vendors cannot access one another’s code, and the drone manufacturer cannot extract or copy a vendor’s software. Phantom execution, where the code exists only in RAM, combined with a hardware security module, ensures protection even with physical access to the device.











